mirror of
https://github.com/bitwarden/browser.git
synced 2024-12-22 16:29:09 +01:00
* [EC-598] feat: scaffold content scripting * [EC-598] feat: load page script from content script * [EC-598] feat: succesfully intercept methods * [EC-598] feat: add better support for messaging * [EC-598] feat: implement calls to new service * [EC-598] feat: add ability to return responses * [EC-598] feat: half-implemented params mapping * [EC-598] feat: add b64 conversion * [EC-598] feat: half-implemented user interfacing * [EC-598] feat: initial working user verification * [EC-598] feat: center popup * [EC-598] feat: add basic cancel button * [EC-598] feat: confirm new credentials * [EC-598] feat: add cbor-redux npm package * [EC-598] feat: initial version of credential creation * [EC-598] feat: fully working credential creation * [EC-598] feat: fully working register and assert flow * [EC-598] feat: properly check for presence * [EC-598] feat: rudimentar error handling * [EC-598] feat: transparent passthrough of platform authenticators * [EC-598] feat: improve error handling * [EC-598] feat: use browser as fallback when vault does not contain requested credential * [EC-598] feat: add fido2Key to cipher * [EC-598] feat: successfully store passkeys in vault * [EC-598] feat: implement passwordless vault auth * [EC-598] feat: add basic support for managing passkeys * [EC-598] feat: show new cipher being added * [EC-598] feat: allow user to pick which credential to use * [EC-598] feat: differntiate between resident auth and 2fa * [EC-598] feat: add some padding to popout * [EC-598] feat: allow storage of more information * [EC-598] feat: show user name as sub title * [EC-598] feat: show all available data * [EC-598] chore: clean up console logs * [EC-598] feat: fix google issues Google does not like self-signed packed format. I've removed the attestation statement all-together untill further notice. We're don't really have any statements so * [EC-598] fix: temporarily remove origin check * [EC-598] fix: user interaction not being awaited sometimes Only one handler can return a response. That handler needs to return true to indicated it's intention to eventually do so. Our issue was that multiple handlers were returning truthy values, causing a race condition. * [EC-598] fix: messenger crashing The messenger is listening to all DOM communcation, most of which is formatted differently. We were not handling these cases properly which resulted in attempts to access undefined fields. * [EC-598] feat: add basic test-case for messenger * [EC-598] feat: add test for request/response * [EC-598] feat: add initial one-way support for aborting * [EC-598] feat: add ability to throw errors across messenger * [EC-598] feat: transition to using exceptions * [EC-598] feat: add abort controller all the way to service * [EC-598] feat: ability to abort from page script * [EC-598] feat: add automatic default timeouts * [EC-598] chore: move component from generic popup fodler * [EC-598] chore: collect all passkeys stuff under common folder * [EC-598] fix: filter messages from other sources * [EC-598] chore: add small todo comment * [EC-598] feat: add timeout and UV to params * [EC-598] feat: implement full support for timeouts * [EC-598] feat: start creating separate authenticator service * [EC-598] feat: first tested rule in new authentitcator * [EC-598] feat: allow user to confirm duplication * [EC-598] feat: add check for unsupported algorithms * [EC-598] feat: add check for invalid option values * [EC-598] feat: handle unsupported pinAuth * [EC-598] feat: confirm new credentials * [EC-598] feat: rearrange order of execution * [EC-598] chore: rearrange tests * [EC-598] feat: add support for saving discoverable credential * [EC-598] feat: remove ability to duplicate excluded credentials * [EC-598] chore: rearrange tests * [EC-598] feat: add support for non-discoverable credentials * [EC-598] chore: use webauthn authenticator model as base instead of CTAP * [EC-598] feat: don't leak internal errors during creation * [EC-598] feat: tweak key data to contain separate type and algorithm * [EC-598] feat: add counter to fido2key * [EC-598] feat: complete implementation of `makeCredential` * [EC-598] feat: add ignored enterpriseAttestation param * [EC-598] feat: start implementing `getAssertion` * [EC-598] feat: add separate `nonDiscoverableId` to keys * [EC-598] fix: properly convert credentials to guid raw format * [EC-598] chore: add todo tests about deleted items * [EC-598] feat: implement missing credential checks * [EC-598] feat: add user confirmation test to assertion also rewrite to use cipher views in tests * [EC-598] feat: increment counter during assertion * [EC-598] feat: implement assertion * [EC-598] feat: add signatures to attestation * [EC-598] feat: add general error handling for attestation * [EC-598] feat: start working on new `Fido2ClientService` * [EC-598] feat: check user id length * [EC-598] feat: check origin and rp.id effective domains * [EC-598] feat: check for supported key algorithms * [EC-598] feat: hash client data and throw if aborted * [EC-598] feat: extend return from authenticator * [EC-598] feat: fully implement createCredential * [EC-598] feat: implement assertCredential * [EC-598] feat: make everything compile again * [EC-598] feat: remove orgigin * [EC-598] fix: rpId validation logic * [EC-598] fix: some smaller bugs * [EC-598] fix: flag saying authData doesnt contain attestation * [EC-598] fix: wrong flags in tests * [EC-598] fix: data not getting saved properly * [EC-598] fix: invalid signature due to double hashing * [EC-598] chore: clean up unusued function * [EC-598] feat: fully wokring non-discoverable implementation * [EC-598] feat: add initial implementation of UI sessions * [EC-598] feat: fully refactored user interface Now uses sessions instead of single request-response style communcation * [EC-598] feat: make fallback working again * [EC-598] feat: add rudimentary support for excluded credentials * [EC-598] fix: send correct excluded cipher ids * [EC-598] feat: wait for session close before closing window * [EC-598] feat: test unique signatures * [EC-598] chore: clean up old commented code * [EC-598] feat: do not exclude organization credentials * [EC-598] chore: remove unused clas * [EC-598] fix: remove platform attachment check * [EC-598] chore: rename webauthn folder to fido2 * [EC-598] chore: continue rename webauthn to fido2 * [EC-598] feat: interpret rk preferred as required Fixes GoDaddy issues * [EC-598] fix: bug preventing fallback on assertion * [EC-598] feat: inform user when no credentials are found * [EC-598] chore: add some more console logs for debugging * [EC-598] feat: very basic scroll when picking credentials * [EC-598] chore: tweak unique signature test * [EC-598] chore: tweak how unassigned rpId gets calcuated * [EC-598] fix: response prototype chains * [EC-598] feat: allow discoverable credentials to be used for non-discoverable assertions * [EC-598] fix: counter not being saved correctly * [EC-598] fix: bug in result mapping * [EC-598] feat: add support for user verifiction using MP during attestation * [EC-598] feat: add support for user verifiction using MP during assertion * [EC-598] feat: quick fix noop service * [EC-598] chore: refactor observables a little bit * [EC-598] feat: show unsupported user verification error * [EC-598] feat: add logging to fido2 authenticator * [EC-598] feat: add logging to fido2 client * [EC-598] feat: close popout directly from bg script * [EC-598] chore: clean up page-script * [EC-598] feat: add webauthn polyfill * [EC-598] feat: polyfill platform authenticator support * [EC-598] feat: only show fallback options if supported * [EC-598] fix: reponse not correctly polyfilled * [EC-598] chore: add name to polyfill classes * [EC-598] chore: update unsupported UV copy * [EC-598] fix: race condition when opening new popout * Fixed lint issues * [PM-1500] Add feature flag to enable passkeys (#5406) * Added launch darkly feature flag to passkeys implementation * fixed linter * Updated fido2 client service test to accomodate feature flag * Updated fido2client service to include unit test for feature flag * Renamed enable pass keys to fido2 vault credentials, added unit test when feature flag is not enabled * fixed failing Login domain test case * [EC-598] chore: remove unecessary return statement * [EC-598] chore: remove unnecessary eslint disable * [PM-1975] Move FIDO2 files into vault folder (#5496) * Moved fido2 models to vault in libs * Moved fido2 models to vault in libs * Moved fido2 services and abstractions to vault folder in libs * Moved fido2 popup to vault folder on the browser * Updated import path after moving files to the vault folder * Moved authenticator abstraction and service to the vault folder * Updated content and page script path * Added content script, page script and background messaging to vault * fixed lint issue * Updated reference paths * Added missing fallbacksupported property in test files * Added missing fallbacksupported to the newSession method * [PM-2560] Fix Firefox default passkeys handling (#5690) * Return callback response in addListener * Add clarifying comment * Isolate returning the callback to fido2 commands * Update apps/browser/src/platform/browser/browser-api.ts Co-authored-by: Cesar Gonzalez <cesar.a.gonzalezcs@gmail.com> * Fix formatting --------- Co-authored-by: Cesar Gonzalez <cesar.a.gonzalezcs@gmail.com> * [PM-1976] Display passkeys properly on the browser (#5616) * Removed passkeys from the vault types filter and added fucntion to get the count of Fido2keys and Login types * Updated build filter to take Fido2key type as a Login type * Updated icon font files * Updated vault items and view to handle changes with fido2keys * Updated add edit view for fido2keys * Prevent moving passkeys to an organization where it exists * Prevent moving passkeys to an organization where it exists * Added view for non-discoverable passkeys * Added diaglog to inform user that passkey won't be copied when cloning a non discoverable key * Muted text that shows cipher item is available for 2fa * Changed conditional to check if an organization already has the same passkey item * Muted text to align with figma designs and used rpId for the application input value * Modified checkFido2KeyExistsInOrg function to workk with discoverable and non discoverable keys * Differentiate between non-discoverable and discoverable keys when moving to an organization * Added suggested changes from PR review * Updated font files css changes * Fixed bug preventing launch bitton from working for Login types (#5639) * [PM-1574] Display passkeys on web (#5651) * Allowed discoverable Fido2key type to be displayed alongside Login type * Added view during edit for discoverable and non-discoverable passkeys * Fixed PR comments, added relvant tests to domain changes * Fixed imports and updated the launch function to use the Launchable interface * Added launch on vault filter for fido2key types * Added missing passkey text field in edit view (#5800) * [PM-1977] Display passkeys properly on the desktop (#5763) * Allowed discoverable Fido2key type to be displayed alongside Login type * Added view during edit for discoverable and non-discoverable passkeys * Fixed PR comments, added relvant tests to domain changes * Fixed imports and updated the launch function to use the Launchable interface * Added fido2key to login filter and added view display for fido2key * Added passkeys view for non discoverable passkeys and edit view for passkeys * Fixed PR comments * switched date format to short * [PM-3046] [PM-3047] Defects for discoverable and non-discoverable passkeys on desktop and web (#5847) * Added missing passkey text field in edit view (#5800) * Added dialog to clone no discoverable passkeys on web and desktop.Also, removed clone on the desktop for discoverable passkeys and added passkey view to non- discoverable passkeys on desktop during edit * Prevent cloning dialog on non fido2key ciphers * Made fido2key use website favicon if avaialble instead of the passkey icon * Do not display passkey view on clone edit for dekstop * Do not display passkey view on clone edit for browser * Prevented movement of passkeys ND or D to an organization once one exists and also made it possible for org memebers with user roles to move passkeys to an organization. (#5868) * two step passkey view was outside the conditional (#5872) * fixed merge conflict * [PM-2907] Shopify Passkey Broken on Firefox When Extension is Installed (#6003) * [PM-2907] Shopify Passkey Broken on Firefox When Extension is Installed * [PM-2907] Shopify Passkey Broken on Firefox When Extension is Installed * [PM-2907] Shopify Passkey Broken on Firefox When Extension is Installed * Added passkey fallback imaged and added extension to image name on the icons component * [PM-3155] CLI: Editing a cipher with a non-discoverable passkey causes the passkey to be removed (#6055) * Added fido2keyexport for the CLI and added the fido2key field to the login response for the CLI * Added fido2keyexport for the CLI and added the fido2key field to the login response for the CLI * Removed unneccesary code * Added non discoverable passkey to template * [PM-2270] Renamed Fido2Key.userName to Fido2Key.userDisplayName (#6005) * Renamed fido2key property username to userDisplayName * Renamed username property on fido2key object to userdisplayname * updated username to userDisplayName in fido2 export * Update libs/angular/src/vault/vault-filter/models/vault-filter.model.ts Co-authored-by: Oscar Hinton <Hinton@users.noreply.github.com> * [PM-3775] feat: import v0.4.0 (#6183) * [PM-3660] Address PR feedback (#6157) * [PM-3660] chore: simplify object assignment * [PM-3660] fix: remove unused origin field * [PM-3660] feat: add Fido2Key tests * [PM-3660] chore: convert popOut to async func * [PM-3660] chore: refactor if-statements * [PM-3660] chore: simplify closePopOut * [PM-3660] fix: remove confusing comment * [PM-3660] chore: move guid utils away from platform utils * [PM-3660] chore: use null instead of undefined * [PM-3660] chore: use `switch` instead of `if` * [EC-598] fix: popup not closing bug * [PM-1859] Refactor to credentialId (#6034) * PM-1859 Refactor to credentialId * PM-1859 Minor changes * PM-1859 Fix credentialId initialization logic * PM-1859 Added missing logic * PM-1859 Fixed logic to use credentialID instead of cipher.id * [PM-1859] fix: missing renames --------- Co-authored-by: Andreas Coroiu <andreas.coroiu@gmail.com> * [PM-1722] gracefully fail if site prompts user for passkey on load (#6089) * added error logic to look for options.mediation in page-script * moved the options mediation logic into the try catch. changed error to FallbackRequestedError * [PM-1224] Ensure Passkeys Not Requested From Iframes (#6057) * added isNotIFrame method to page-script * added NotAllowedError to assertCredential in fido2 * remove excess comments * refactor fido2-client.service. created new errorhandling method for similar code between create and assert * update types and naming convention for new method in fido2-client.service * Did a reset to previous commit withiout the refactoring to reduce code duplication, Renamed isNotIframeCheck function and fixed other commits * Revert "update types and naming convention for new method in fido2-client.service" This reverts commit |
||
|---|---|---|
| .. | ||
| .vscode | ||
| config | ||
| scripts | ||
| src | ||
| .dockerignore | ||
| .eslintrc.json | ||
| .gitignore | ||
| config.js | ||
| crowdin.yml | ||
| dev-server.shared.pem | ||
| Dockerfile | ||
| entrypoint.sh | ||
| jest.config.js | ||
| package.json | ||
| postcss.config.js | ||
| README.md | ||
| tailwind.config.js | ||
| test.setup.ts | ||
| tsconfig.json | ||
| tsconfig.spec.json | ||
| webpack.config.js | ||
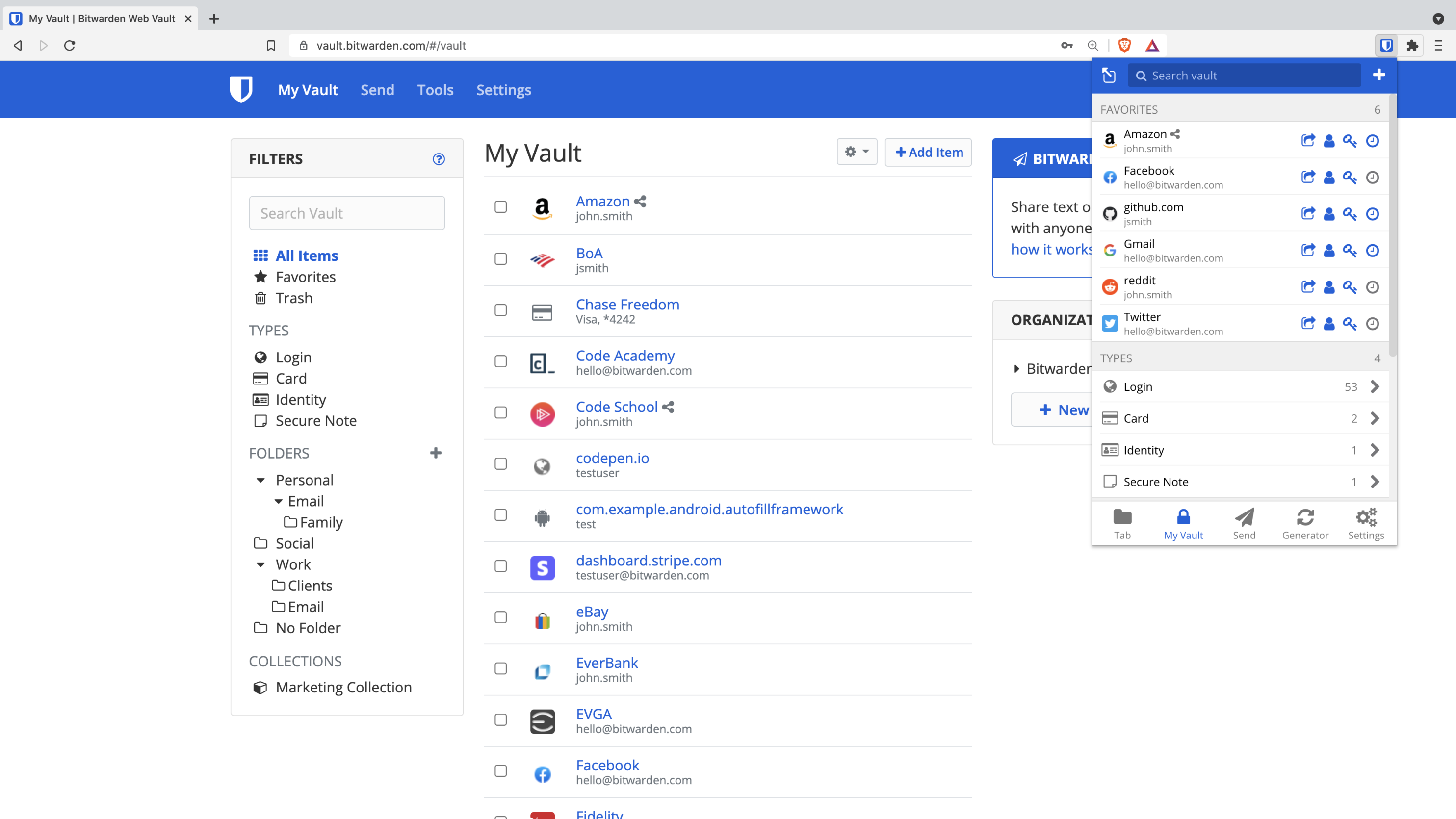
The Bitwarden web project is an Angular application that powers the web vault (https://vault.bitwarden.com/).
Documentation
Please refer to the Web vault section of the Contributing Documentation for build instructions, recommended tooling, code style tips, and lots of other great information to get you started.

